Elastic Security Health Check: What It Really Tells You About Your Detection Stack
Security teams often assume their tools are working because alerts are firing. Dashboards look busy. Data is flowing. There is movement. That surface activity can be misleading.
An Elastic Security Health Check forces a different conversation. It shifts attention from visible noise to operational integrity. Not whether Elastic is installed, but whether it is functioning as intended under pressure.
Elastic deployments tend to grow organically. A few agents here. A new integration there. Detection rules imported, then tweaked, then forgotten. Over time, the estate becomes uneven. Some hosts report cleanly. Others drift out of compliance. Logging pipelines choke silently. Analysts compensate without realising they are compensating. The platform rarely fails loudly. It degrades quietly. A structured review of Elastic Security exposes those silent degradations before an incident does.
Visibility Is Not Coverage
Most environments claim full coverage. That usually means an agent exists on most endpoints. Coverage is not the same as visibility.
An elastic security health check examines whether telemetry is complete, consistent, and trustworthy. It looks at ingestion rates over time. Checks for gaps in log streams. It questions whether key data sources are still feeding the cluster after infrastructure changes.
Consider what happens when a domain controller rebuild takes place. The server returns to production. Authentication works. Users log in. Meanwhile, audit logging has reverted to default settings. Elastic continues collecting logs, just not the ones that matter.
Weeks pass before anyone notices.
A health check inspects those blind spots deliberately. It correlates expected log volume with actual intake. Validates event categories against detection logic. It highlights systems that have gone quiet without being decommissioned.
That quietness is often the first sign of risk.
Detection Engineering Drift
Detection rules accumulate over time. Some are imported from Elastic’s rule packs. Others are written internally. A few are copied from community repositories and lightly edited.
Then environments change.
New applications appear. Legacy services retire. Operating systems are patched. Cloud configurations evolve. Detection rules remain static unless someone maintains them.
An elastic security health check evaluates rule efficacy rather than simply counting how many exist. It reviews alert volumes against baseline behaviour. Identifies noisy rules that analysts routinely close without investigation. It surfaces high value rules that have not triggered in months and may no longer align with reality.
There is also the issue of dependency. Many rules rely on specific fields or enrichment data. If ingest pipelines alter, or if index mappings shift, those dependencies break. The rule still runs. It just returns nothing useful.
This kind of silent failure rarely appears on executive dashboards.
The purpose of reviewing detection health is not to inflate alert numbers. It is to ensure the logic still reflects the threat landscape and the organisation’s actual architecture.
Cluster Performance and Stability
Security conversations often stay at the detection layer. Yet performance at the cluster level shapes the entire security posture.
Elastic environments under strain behave unpredictably. Query latency increases. Dashboards stall. Analysts hesitate before pivoting between indices. That friction changes investigative behaviour.
An elastic security health check inspects shard allocation, node utilisation, index lifecycle policies, and storage growth trends. It checks whether hot, warm, and cold tiers are configured according to data value rather than convenience.
There is a subtle but important relationship between cost management and security resilience. Organisations sometimes reduce retention to control storage costs. They shorten index lifecycles without adjusting investigative expectations.
Six months later, an incident response team attempts to trace lateral movement across a timeline that no longer exists.
Performance tuning and retention strategy should not be separate from security discussion. They are tightly connected.
Identity and Access Configuration
Access control within Elastic itself is frequently overlooked. Role based access exists. Spaces are defined. Yet permissions often expand gradually.
Temporary access becomes permanent. Administrative roles multiply. Service accounts accumulate privileges beyond necessity.
A proper review looks at user roles, API keys, integration permissions, and cross cluster trust settings. It asks whether least privilege still applies. It checks whether former contractors retain access through overlooked tokens.
These details rarely cause immediate disruption. They become relevant during an insider event or when an attacker pivots from a compromised account.
The health of the security platform includes the security of the platform.
A Practical Framework for an Elastic Security Health Check
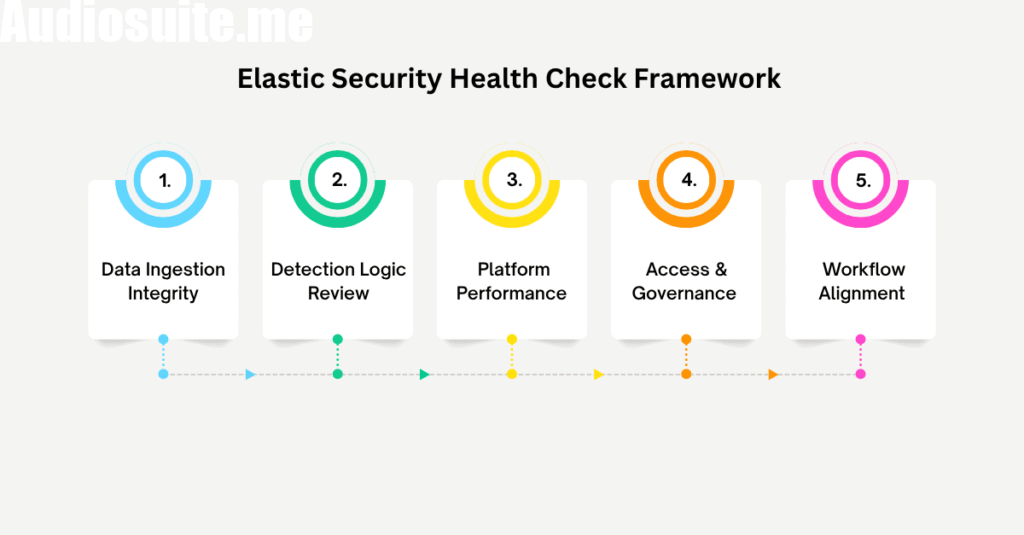
Before reviewing technical findings, it helps to break the assessment into defined layers.
- Data Ingestion Integrity
Validate agent deployment status, integration health, pipeline processing, and event completeness. Compare expected versus actual log volumes. Identify silent hosts.
- Detection Logic Review
Analyse rule performance, alert quality, false positive trends, and dependency alignment. Remove redundant or obsolete rules. Adjust thresholds based on current behaviour.
- Platform Performance and Storage
Examine cluster health, shard balance, node resource usage, and index lifecycle policies. Confirm retention aligns with investigation requirements.
- Access and Governance Controls
Audit user roles, API keys, service accounts, and external integrations. Confirm principle of least privilege. Remove dormant access paths.
- Operational Workflow Alignment
Assess how analysts interact with the platform. Review case management, escalation pathways, and integration with ticketing systems. Identify friction points that slow investigation.
Each layer informs the next. Skipping one creates distortion. Strong detection logic cannot compensate for missing data. Clean ingestion cannot offset poor governance.
The framework encourages systematic review rather than reactive patching.
Real World Patterns Observed in Mature Environments
Across established organisations, similar patterns appear.
Elastic is deployed as part of a transformation programme. Initial enthusiasm drives careful configuration. After go live, attention shifts to other priorities. The platform continues running. Minor issues accumulate.
Security teams adapt informally. They learn which alerts to ignore. Rrely on tribal knowledge about which hosts tend to drop logs. They build workarounds.
Over time, the informal understanding becomes embedded practice. No one questions it because the system appears stable.
Then a significant incident occurs. Investigation reveals data gaps. Certain telemetry was missing for weeks. A critical rule was disabled during troubleshooting and never re enabled.
The issue was not tool capability. It was the absence of structured review.
An Elastic Security Health Check resets that baseline. It reintroduces disciplined scrutiny without implying failure. It treats the platform as a living system rather than a static deployment.
The Strategic Value of Periodic Review
Technology estates do not remain static. Mergers, cloud migrations, regulatory shifts, and workforce changes alter risk profiles constantly.
Security tooling must evolve accordingly. Elastic is flexible, but flexibility demands oversight.
Periodic health checks introduce measured friction. They force teams to pause and evaluate assumptions. They also provide evidence for budget and architectural decisions. When cluster strain or ingestion gaps are documented clearly, remediation conversations become grounded rather than speculative.
There is another aspect. External stakeholders, including auditors and board members, increasingly ask for proof of detection capability. Not just tool presence.
A documented Elastic Security Health Check demonstrates operational maturity. It shows that the organisation does not rely on default settings or inherited configurations.
It signals intent.
Conclusion
An elastic security health check is less about configuration review and more about operational truth. It examines whether data is complete, detection logic is relevant, performance is stable, and governance is intact. It reveals the difference between a deployed platform and a dependable one.
Organisations often delay this work because nothing appears broken. The absence of visible failure feels reassuring. Experience suggests otherwise. Gaps tend to surface under pressure, not during routine operations. Often, an expert perspective can help. CyberNX is a reliable elastic stack services partner that can help you strategically deploy elastic security for comprehensive security monitoring, ransomware protection, malware protection, and other critical capabilities.
Disclaimer
The information provided in this article is for general informational and promotional purposes only. While every effort has been made to ensure accuracy, plumbing and gas systems can vary significantly based on property type, local regulations, and environmental conditions. Readers are encouraged to consult directly with licensed professionals, such as Simply Plumbing and Gas, for assessments, repairs, or installations specific to their situation. The article does not constitute professional engineering, plumbing, or safety advice, and the publisher is not responsible for any actions taken based on the content provided.






